COMPUTER NETWORKS CHAPTER 3 NETWORK LAYER NOTES CSE 3RD year sem 1
- 1. CS503PC: COMPUTER NETWORKS UNIT - III Network Layer: Design issues, Routing algorithms: shortest path routing, Flooding, Hierarchical routing, Broadcast, Multicast, distance vector routing, Congestion Control Algorithms, Quality of Service, Internetworking, The Network layer in the internet. 1
- 2. UNIT - III The Network Layer Routing Algorithms, Congestion Control Algorithms, QoS
- 3. Network Layer Design Issues • Store-and-forward packet switching • Services provided to transport layer • Implementation of connectionless service • Implementation of connection-oriented service • Comparison of virtual-circuit and datagram networks
- 4. Store-and-Forward Packet Switching The environment of the network layer protocols. ISP’s equipment
- 5. Services Provided to the Transport Layer 1. Services independent of router technology. 2. Transport layer shielded from number, type, topology of routers. 3. Network addresses available to transport layer use uniform numbering plan – even across LANs and WANs
- 6. Implementation of Connectionless Service Routing within a datagram network ISP’s equipment A’s table (initially) A’s table (later) C’s Table E’s Table
- 7. Implementation of Connection-Oriented Service Routing within a virtual-circuit network ISP’s equipment A’s table C’s T able E’s Table
- 8. Comparison of Virtual-Circuit and Datagram Networks Comparison of datagram and virtual-circuit networks
- 9. Routing Algorithms • Routing is a process of transferring the packets from source m/c to destination machine, while routing algorithms (RA) are s/w responsible for deciding which outgoing line an incoming packet should be transmitted on. • The purpose of RA is to decide which route is to be followed by a packet on the basis of following parameters: • Availability of channels (paths/links/routes) • Link transmission delay • Traffic intensity, and • Capacity (bandwidth) of the link
- 10. Routing Algorithms • On the basis of nature of information used in the algorithm, Routing Algorithms are categorized into two classes: • Non-Adaptive: These do not base their routing decisions on the measurements/estimates of current traffic or topology, instead the choice of route to get from node ‘I’ to node ‘j’ is computed in advance or off-line, and hence also called as ‘Static Routing’ or ‘Pre- determined Routing’. • Adaptive: It attempts to change their routing decisions to reflect changes in topology and the current traffic. • • • • On the basis of scope of information used in the algorithm, Routing Algorithms are classified into three types: Centralized Routing: The global algorithm uses information collected from the entire subnet in an attempt to make optimal decision. Isolated Routing: The local algorithm runs separately on each IMP(Interface Message Processor) and uses information only available there e.g., queue length. DistributedRouting: These use information availablelocally as well as information available at their neighbors.
- 11. Routing Algorithms Properties of the R.A. Simplicity: The algorithm should not use very complex features. Correctness: The algorithm should clearly say about the start and end of the route searching. Robustness: The algorithms should either be capable of correcting smaller mistakes or displaying message to the user to correct errors (Detection and Corrections) Stability: In the event of failure of one or few IMPs, the total system should not be crashed or down. Fairness: Nothing should be ambiguous, everything should be stated clearly and the algorithms should not lead to congestion. Optimality: The algorithms should ensure to minimize the mean packet delay time as well as maximize the total throughput of the network (maximum number if message transmission with minimum delay).
- 12. Routing Algorithms • Optimality principle • Shortest path algorithm • Flooding • Distance vector routing • Link state routing • Routing in ad hoc networks • Broadcast routing • Multicast routing • Anycast routing • Routing for mobile hosts • Routing in ad hoc networks
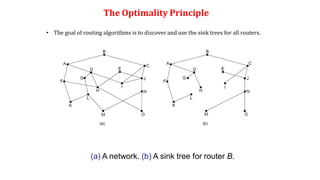
- 13. The Optimality Principle • If Path from A to B is Optimal then, If any Router exist between A & B i.e C then path from A to C and C to B will be Optimal A B A B C Optimal Path Optimal Path Optimal Path
- 14. The Optimality Principle (a) A network. (b) A sink tree for router B. • The goal of routing algorithms is to discover and use the sink trees for all routers.
- 15. Shortest Path Algorithm (1) This algorithm finds the shortest path between any two given nodes on the basis of any of the following (metrics/functions): • Number of hops • Distance • Avg. traffic In general, the labels of the arcs can be function of distance, bandwidth, average traffic, communication cost, mean queuing delay or transmission delay. Many algorithms may be designed using these parameters. One such algorithms is designed by Dijkstra (1959) to determine the shortest path between two nodes. • Communication cost • bandwidth • Geographicaldistance • Mean queuing delay, etc.,.
- 16. Shortest Path Algorithm (1) Steps of Dijkstra’s SPA algorithm to determine the shortest path between two nodes: 1. Initially, no path is known. So all the nodes are labeled as at an infinite distance from source node. 2. As the algorithm proceeds, the labels of the nodes changes accordingly reflecting a better path from the given source to the given sink. 3. Start from a node, and examine all adjacent node(s) to it. If the sum of labels of nodes and distance from working node to the node being examined is less than the label on that node, then we have a shortest path, and the node is re-labeled. In a similar fashion, all the adjacent nodes to the working node are inspected and the tentative labels are changed. If possible the entire graph is searched for tentatively labeled nodes with the smallest value, the node is made the permanent node. With the progress of the algorithm, all permanent nodes are encircled, so the shortest path could be reconstructed.
- 17. Shortest Path Algorithm (1) The first five steps used in computing the shortest path from A to D. The arrows indicate the working node L(B) = min(∞, 0+2)= 2 L(G) = min(∞, 0+6)= 6 L(C) = min(∞, 2+7)=9 L(E) = min(∞, 2+2)= 4 L(F) = min(∞, 4+2)= 6 L(G) = min(∞, 4+1)= 5
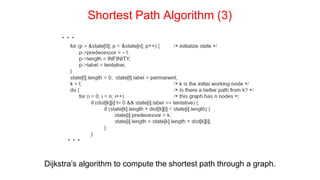
- 18. Shortest Path Algorithm (2) . . . Dijkstra’s algorithm to compute the shortest path through a graph.
- 19. Shortest Path Algorithm (3) . . . Dijkstra’s algorithm to compute the shortest path through a graph. . . .
- 20. Shortest Path Algorithm (4) . . . Dijkstra’s algorithm to compute the shortest path through a graph.
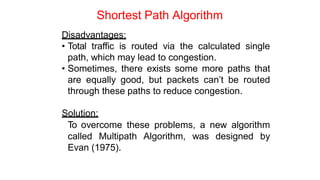
- 21. Shortest Path Algorithm Disadvantages: • Total traffic is routed via the calculated single path, which may lead to congestion. • Sometimes, there exists some more paths that are equally good, but packets can’t be routed through these paths to reduce congestion. Solution: To overcome these problems, a new algorithm called Multipath Algorithm, was designed by Evan (1975).
- 22. Other Routing Algorithms a) Baran’s Hot Potato Algorithm (1964): Isolated routing, also called as Shortest Queue Algorithm. As soon as a node receives a packet, it tries to get rid of it by putting/forwarding it to the line having shortest queue. b) Flooding: Each incoming packet is forwarded to every outgoing line, thereby ensuring shortest path and shortest transmission delay. But, operative for very low traffic condition. c) Centralized Routing using RCC: All IMPs in the network periodically sends information to Routing Control Centre (RCC), regarding their queue length, delay offered, list of neighbors that are up, etc. Based on these information, RCC computes the routing table global and distributes to all IMPs. It was used in TYMNET in 1971.
- 23. (a) A network. (b) Input from A, I, H, K, and the new routing table for J. Distance Vector Routing
- 26. 1. The Count-to-Infinity Problems 2. Delay metric was queue length, it did not take line bandwidth into account, when choosing routes. Initially all the lines were 50 kbps, and hence no problem, but later some were upgraded to 230 kbps, and others to 1.544 Mbps.
- 27. Link State Routing (IS-IS, OSPF) 1. Discover neighbors, learn network addresses (Hello). 2. Set/Measure distance/cost metric to each neighbor (Echo). 3. Construct packet telling all it has learned. 4. Send packet to, receive packets from other routers (trickiest part, flooding(to check flooding, packet seq. no. and age are used)). 5. Compute shortest path to every other router (Dijkstra’s Algorithm).
- 28. Learning about the Neighbors (1) Nine routers and a broadcast LAN.
- 29. Learning about the Neighbors (2) A graph model of previous slide.
- 30. Building Link State Packets (a) A network. (b) The link state packets for this network.
- 31. Distributing the Link State Packets The packet buffer for router B in previous slide
- 34. Broadcast Routing Reverse path forwarding. (a) A network. (b) A sink tree. (c) The tree built by reverse path forwarding.
- 35. Multicast Routing (1) (a) A network. (b) A spanning tree for the leftmost router. (c) A multicast tree for group 1. (d) A multicast tree for group 2.
- 36. Multicast Routing (2) (a) Core-based tree for group 1. (b) Sending to group 1.
- 37. Anycast Routing (a) Anycast routes to group 1. (b) Topology seen by the routing protocol.
- 38. Routing for Mobile Hosts Packet routing for mobile hosts
- 39. Routing for Mobile Hosts
- 40. Routing in Ad Hoc Networks (a) Range of A’s broadcast. (b) After B and D receive it. (c) After C, F, and G receive it. (d) After E, H, and I receive it. The shaded nodes are new recipients. The dashed lines show possible reverse routes. The solid lines show the discovered route.
- 41. Congestion Control Algorithms (1) • Approaches to congestion control • Traffic-aware routing • Admission control • Traffic throttling • Load shedding
- 42. Congestion Control Algorithms (2) When too much traffic is offered, congestion sets in and performance degrades sharply.
- 43. Approaches to Congestion Control Timescales of approaches to congestion control
- 44. Traffic-Aware Routing A network in which the East and West parts are connected by two links.
- 45. Traffic Throttling (1) (a) A congested network. (b) The portion of the network that is not congested. A virtual circuit from A to B is also shown.
- 46. Traffic Throttling (2) Explicit congestion notification
- 47. Load Shedding (1) A choke packet that affects only the source..
- 48. Load Shedding (2) A choke packet that affects each hop it passes through.
- 49. Quality of Service • Application requirements • Traffic shaping • Packet scheduling • Admission control • Integrated services • Differentiated services
- 50. Application Requirements (1) How stringent the quality-of-service requirements are. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 51. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 Categories of QoS and Examples 1. Constant bit rate • Telephony 2. Real-time variable bit rate • Compressed videoconferencing 3. Non-real-time variable bit rate • Watching a movie on demand 4. Available bit rate • File transfer
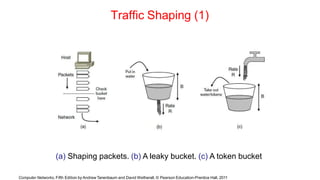
- 52. Traffic Shaping (1) (a) Shaping packets. (b) A leaky bucket. (c) A token bucket Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 53. Traffic Shaping (2) (a) Traffic from a host. Output shaped by a token bucket of rate 200 Mbps and capacity (b) 9600 KB, (c) 0 KB. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 54. Traffic Shaping (3) Token bucket level for shaping with rate 200 Mbps and capacity (d) 16000 KB, (e) 9600 KB, and (f) 0KB.. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 55. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 Packet Scheduling (1) Kinds of resources can potentially be reserved for different flows: 1. Bandwidth. 2. Buffer space. 3. CPU cycles.
- 56. Packet Scheduling (2) Round-robin Fair Queuing Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 57. Packet Scheduling (3) (a) Weighted Fair Queueing. (b) Finishing times for the packets. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 58. Admission Control (1) An example flow specification Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 59. Admission Control (2) Bandwidth and delay guarantees with token buckets and WFQ. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 60. Integrated Services (1) (a) A network. (b) The multicast spanning tree for host 1. (c) The multicast spanning tree for host 2. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 61. Integrated Services (2) (a) Host 3 requests a channel to host 1. (b) Host 3 then requests a second channel, to host 2. (c) Host 5 requests a channel to host 1. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 62. Differentiated Services (1) Expedited packets experience a traffic-free network Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 63. Differentiated Services (2) A possible implementation of assured forwarding Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 64. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 Internetworking • How networks differ • How networks can be connected • Tunneling • Internetwork routing • Packet fragmentation
- 65. How Networks Differ Some of the many ways networks can differ Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 66. How Networks Can Be Connected (a) A packet crossing different networks. (b) Network and link layer protocol processing. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 67. Tunneling (1) Tunneling a packet from Paris to London. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 68. Tunneling (2) Tunneling a car from France to England Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 69. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 Packet Fragmentation (1) Packet size issues: 1. Hardware 2. Operating system 3. Protocols 4. Compliance with (inter)national standard. 5. Reduce error-induced retransmissions 6. Prevent packet occupying channel too long.
- 70. Packet Fragmentation (2) (a) Transparent fragmentation. (b) Nontransparent fragmentation Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 71. Packet Fragmentation (3) Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 72. Packet Fragmentation (4) Fragmentation when the elementary data size is 1 byte (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 73. Packet Fragmentation (5) Fragmentation when the elementary data size is 1 byte (c) Fragments after passing through a size 5 gateway. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 74. Packet Fragmentation (6) Path MTU Discovery Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 75. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 The Network Layer Principles (1) 1. Make sure it works 2. Keep it simple 3. Make clear choices 4. Exploit modularity 5. Expect heterogeneity . . .
- 76. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 The Network Layer Principles (2) . . . 6. Avoid static options and parameters 7. Look for good design (not perfect) 8. Strict sending, tolerant receiving 9. Think about scalability 10.Consider performance and cost
- 77. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 The Network Layer in the Internet (1) • The IP Version 4 Protocol • IP Addresses • IP Version 6 • Internet Control Protocols • Label Switching and MPLS • OSPF—An Interior Gateway Routing Protocol • BGP—The Exterior Gateway Routing Protocol • Internet Multicasting • Mobile IP
- 78. The Network Layer in the Internet (2) The Internet is an interconnected collection of many networks. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 79. The IP Version 4 Protocol (1) The IPv4 (Internet Protocol) header. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
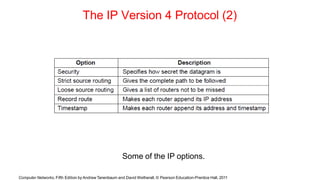
- 80. The IP Version 4 Protocol (2) Some of the IP options. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 81. IP Addresses (1) An IP prefix. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 82. IP Addresses (2) Splitting an IP prefix into separate networks with subnetting. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 83. IP Addresses (3) A set of IP address assignments Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 84. IP Addresses (4) Aggregation of IP prefixes Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 85. IP Addresses (5) Longest matching prefix routing at the New York router. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 86. IP Addresses (6) IP address formats Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 87. IP Addresses (7) Special IP addresses Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 88. IP Addresses (8) Placement and operation of a NAT box. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 89. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 IP Version 6 Goals • Support billions of hosts • Reduce routing table size • Simplify protocol • Better security • Attention to type of service • Aid multicasting • Roaming host without changing address • Allow future protocol evolution • Permit coexistence of old, new protocols. . .
- 90. IP Version 6 (1) The IPv6 fixed header (required). Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 91. IP Version 6 (2) IPv6 extension headers Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 92. IP Version 6 (3) The hop-by-hop extension header for large datagrams (jumbograms). Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 93. IP Version 6 (4) The extension header for routing. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 94. Internet Control Protocols (1) The principal ICMP message types. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 95. Internet Control Protocols (2) Two switched Ethernet LANs joined by a router Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
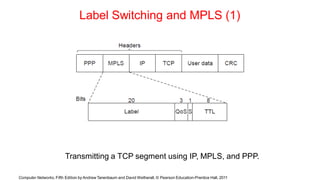
- 96. Label Switching and MPLS (1) Transmitting a TCP segment using IP, MPLS, and PPP. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 97. Label Switching and MPLS (2) Forwarding an IP packet through an MPLS network Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 98. OSPF—An Interior Gateway Routing Protocol (1) An autonomous system Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 99. OSPF—An Interior Gateway Routing Protocol (2) A graph representation of the previous slide. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 100. OSPF—An Interior Gateway Routing Protocol (3) The relation between ASes, backbones, and areas in OSPF. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 101. OSPF—An Interior Gateway Routing Protocol (4) The five types of OSPF messages Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 102. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 BGP—The Exterior Gateway Routing Protocol (1) Examples of routing constraints: 1. No commercial traffic for educat. network 2. Never put Iraq on route starting at Pentagon 3. Choose cheaper network 4. Choose better performing network 5. Don’t go from Apple to Google to Apple
- 103. BGP—The Exterior Gateway Routing Protocol (2) Routing policies between four Autonomous Systems Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 104. BGP—The Exterior Gateway Routing Protocol (3) Propagation of BGP route advertisements Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011
- 105. Computer Networks, Fifth Edition by Andrew Tanenbaum and David Wetherall, © Pearson Education-Prentice Hall, 2011 Mobile IP Goals 1. Mobile host use home IP address anywhere. 2. No software changes to fixed hosts 3. No changes to router software, tables 4. Packets for mobile hosts – restrict detours 5. No overhead for mobile host at home.